The Challenge
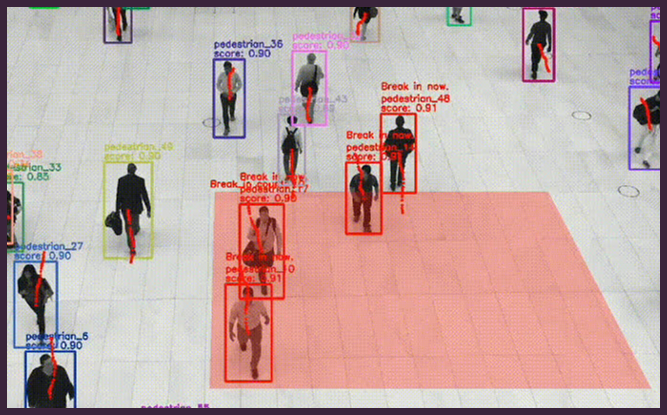
Trespassing into restricted areas, such as construction sites and private properties, poses significant security, safety, and legal risks. Unauthorised access can lead to theft, vandalism, injuries, and operational disruptions. Traditional security measures often fail to detect or respond to intrusions in real-time.